Thoughts on the recent Ethereum smart contracts C2 abuse
Hello all! 👋 It’s been a while since my last post. I wasn’t finding anything exciting to write about — until this story caught my attention.
Recently, I came across an article describing attackers using Ethereum smart contracts as a Command & Control (C2) mechanism. This was interesting because it made me immediately start thinking about different ways to detect such activity.
My initial instinct was to look at the network side of things.
I spun up two projects to interact with Web3:
- One using Python
- One using Node.js
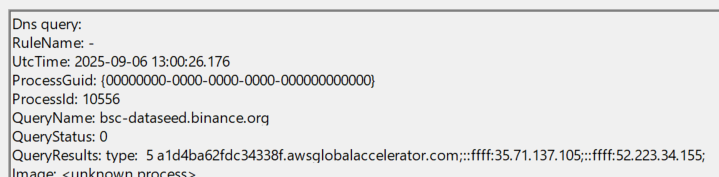
With the Python project, I wrote a script to query Binance’s BSC node for some data tied to a random address. I then reviewed the resulting Sysmon telemetry.
👉 The issue? There are countless nodes, blockchains, and URLs out there. Monitoring based on static URLs doesn’t scale — it’s simply not practical.
Next, I shifted to my Node.js project.
I reviewed the malicious code shared in the article. And — no surprise here — while the attackers were indeed retrieving instructions from an Ethereum smart contract, the underlying mechanism was nothing new, and honestly, oddly simplistic.
The code still relied on endpoint-level functions to execute those instructions.
To validate this, I wrote a simple Node.js script that executed "whoami" using the same exec function the attacker used.
Sure enough, it worked exactly the same way.
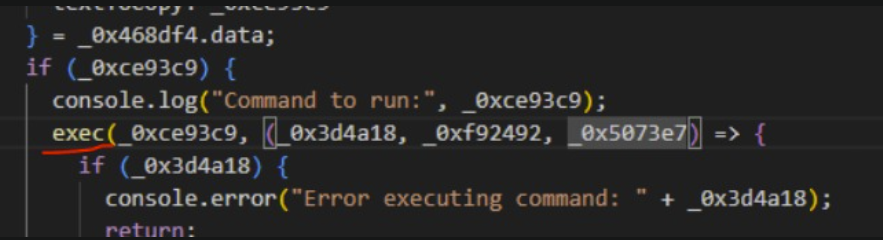

This reinforced my suspicion: instead of chasing down every blockchain node or contract interaction, we can focus on monitoring behaviors we already know how to detect.
The takeaway?
Yes, attackers may use new and shiny techniques — Ethereum smart contracts as C2 is definitely novel.
But in the end, the immutable artifacts often stay the same:
- Suspicious Node.js process behavior
- Unusual command-line execution
- Strange child process creation
These are things we can already detect with solid behavioral rules.
🔑 Lesson: Don’t reinvent the wheel. Stay critical, simulate the activity yourself, and focus on what leaves consistent traces.
If you enjoyed the article, feel free to connect with me!
https://www.linkedin.com/in/daniel-koifman-61072218b/
https://x.com/KoifSec
https://bsky.app/profile/koifsec.bsky.social
https://koifsec.medium.com/
